Neuvector介绍
NeuVector 是最早开发 Docker/Kubernetes 安全产品的公司,是 Kubernetes 网络安全的领导
者,NeuVector 致力于保障企业级容器平台安全,产品适用于各种云环境、跨云或者本地部署等容器生产环境。NeuVector 提供实时深入的容器网络可视化、东西向容器网络监控、主动隔离和保护、容器主机安全以及容器内部安全。和容器管理平台无缝集成并且实现应用级容器安全的自动化。
2021年SUSE收购Neuvector,并将其开源。
项目地址:
https://github.com/neuvector/neuvector
架构解析

NeuVector本身包含Controller、Enforcer、Manager、Scanner、Updater模块。
Controller:整个Neuvector的控制模块,API入口,包括配置下发,高可用主要考虑Controller的HA,通常建议部署3个Controller模块组成集群。
Enforcer:主要用于安全策略部署下发和执行,DaemonSet类型会在每个节点部署。
Manager:提供web-UI(仅HTTPS)和CLI控制台,供用户管理NeuVector。
Scanner:对节点、容器、Kubernetes、镜像进行CVE漏洞扫描
Updater:cronjob,用于定期更新CVE漏洞库
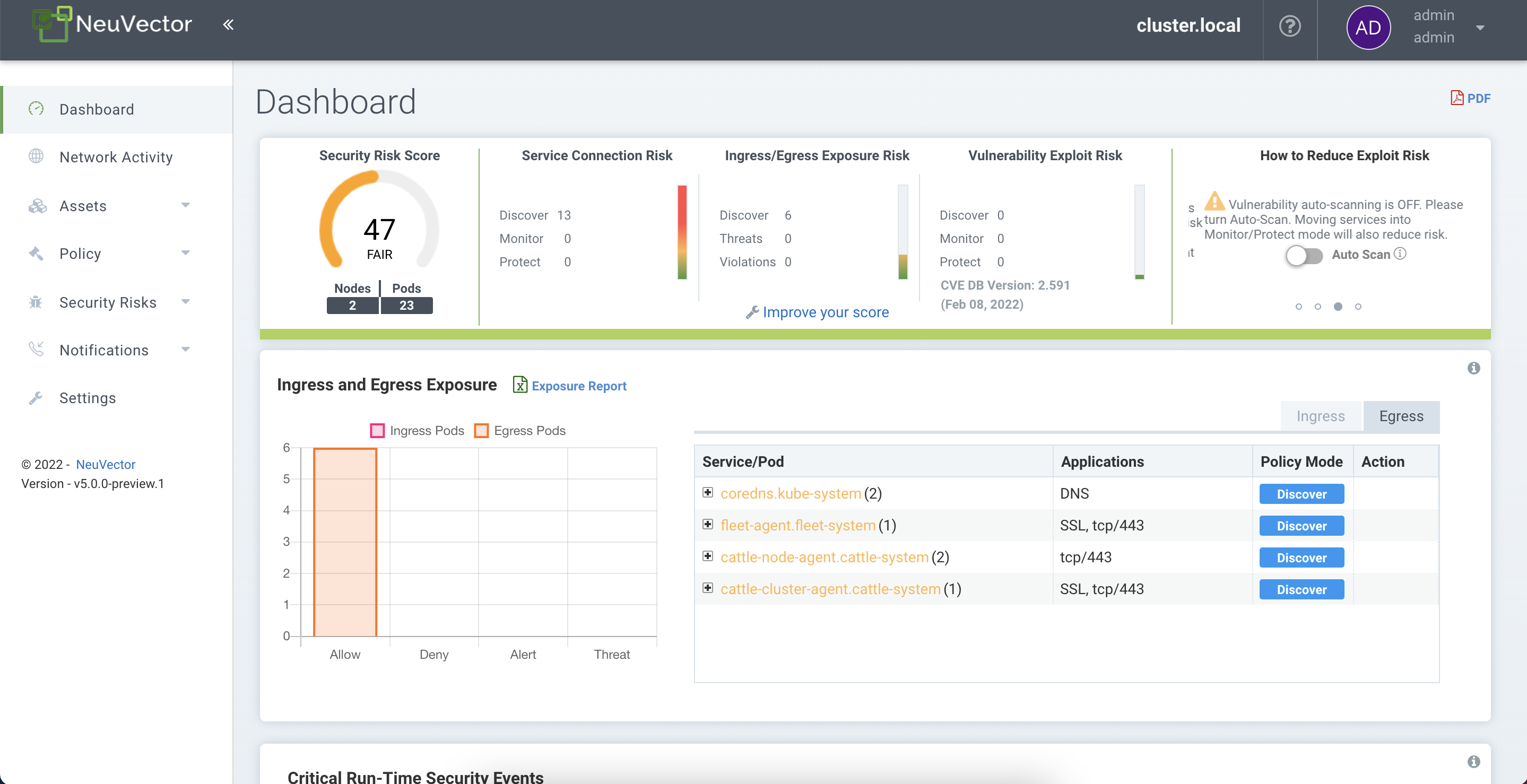
功能介绍
- 安全漏洞扫描
- 容器网络流量可视化
- 网络安全策略定义
- L7防火墙
- CICD安全扫描
- 合规分析
本篇文档更多侧重安装部署,实际功能介绍在后续文章进行深入介绍
NeuVector安装
安装环境
软件版本:
OS:Ubuntu18.04
Kubernetes:1.20.14
Rancher:2.5.12
Docker:19.03.15
NeuVector:5.0.0-b1
快速部署
创建namespace
kubectl create namespace neuvector
部署CRD(Kubernetes 1.19+版本)
1 |
|
部署CRD(Kubernetes 1.18或更低版本)
1 |
|
配置RBAC
1 | kubectl create clusterrole neuvector-binding-app --verb=get,list,watch,update --resource=nodes,pods,services,namespaces |
检查是否有以下RBAC对象
kubectl get clusterrolebinding | grep neuvector
kubectl get rolebinding -n neuvector | grep neuvector
kubectl get clusterrolebinding | grep neuvector
neuvector-binding-admission ClusterRole/neuvector-binding-admission 44h
neuvector-binding-app ClusterRole/neuvector-binding-app 44h
neuvector-binding-customresourcedefinition ClusterRole/neuvector-binding-customresourcedefinition 44h
neuvector-binding-nvadmissioncontrolsecurityrules ClusterRole/neuvector-binding-nvadmissioncontrolsecurityrules 44h
neuvector-binding-nvsecurityrules ClusterRole/neuvector-binding-nvsecurityrules 44h
neuvector-binding-nvwafsecurityrules ClusterRole/neuvector-binding-nvwafsecurityrules 44h
neuvector-binding-rbac ClusterRole/neuvector-binding-rbac 44h
neuvector-binding-view ClusterRole/view 44h
kubectl get rolebinding -n neuvector | grep neuvector
neuvector-admin ClusterRole/admin 44h
部署NeuVector
底层runtime为Docker
kubectl apply -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/neuvector-docker-k8s.yaml
底层runtime为containerd(对于k3s和rke2可以使用此yaml文件)
kubectl apply -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/neuvector-containerd-k8s.yaml
1.21以下的Kubernetes版本会提示以下错误,将yaml文件下载将batch/v1修改为batch/v1beta1
error: unable to recognize "https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/neuvector-docker-k8s.yaml": no matches for kind "CronJob" in version "batch/v1"
1.20.x cronjob还处于beta阶段没有正式GA,1.21版本开始cronjob才进入正式版。
默认部署web-ui使用的是loadblance类型的Service,为了方便访问修改为NodePort,也可以通过Ingress对外提供服务
kubectl patch svc neuvector-service-webui -n neuvector --type='json' -p '[{"op":"replace","path":"/spec/type","value":"NodePort"},{"op":"add","path":"/spec/ports/0/nodePort","value":30888}]'
访问https://node_ip:30888
默认密码为admin/admin
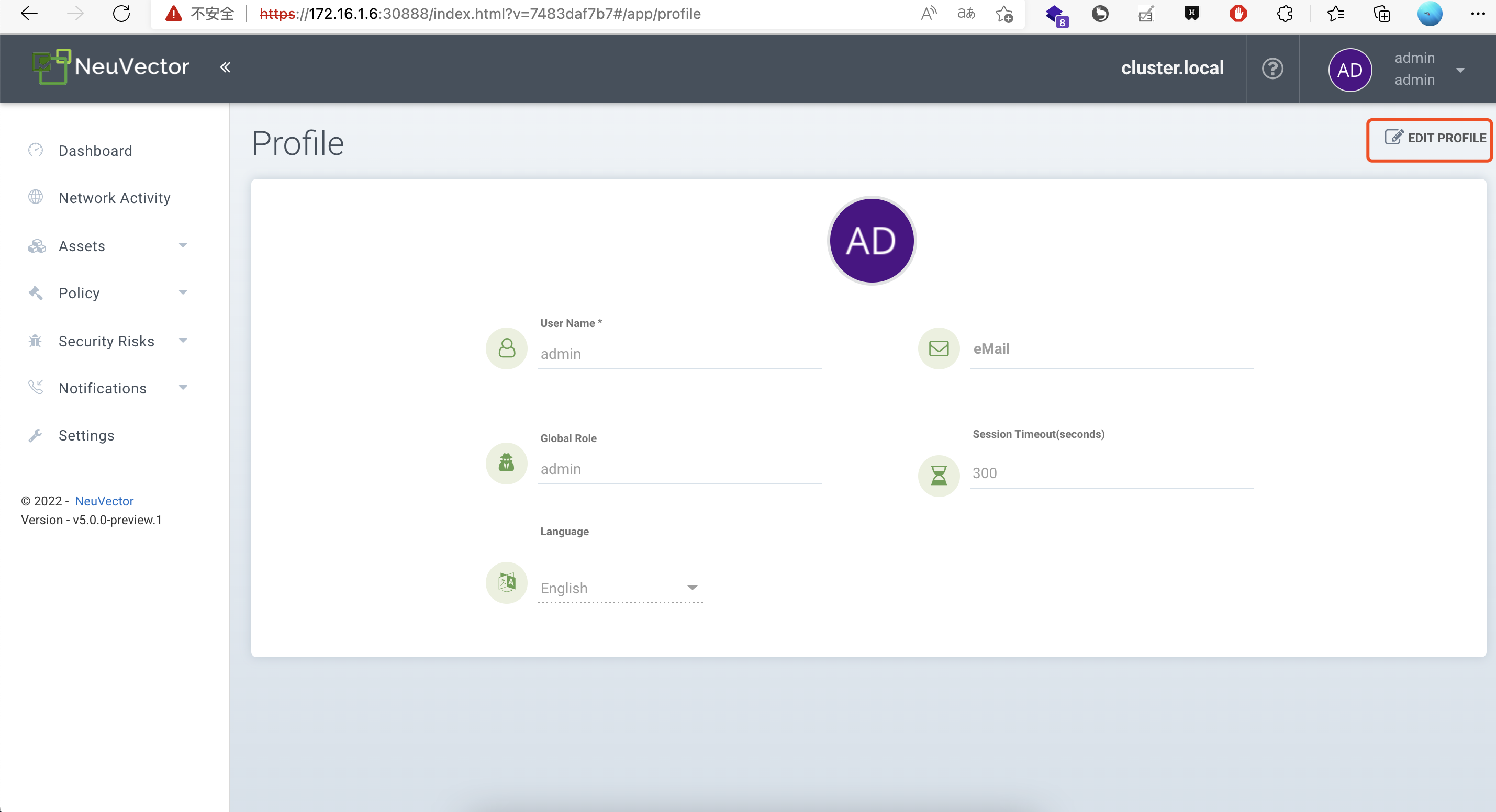
点击头像旁的My profile页面进入设置页面,设置密码和语言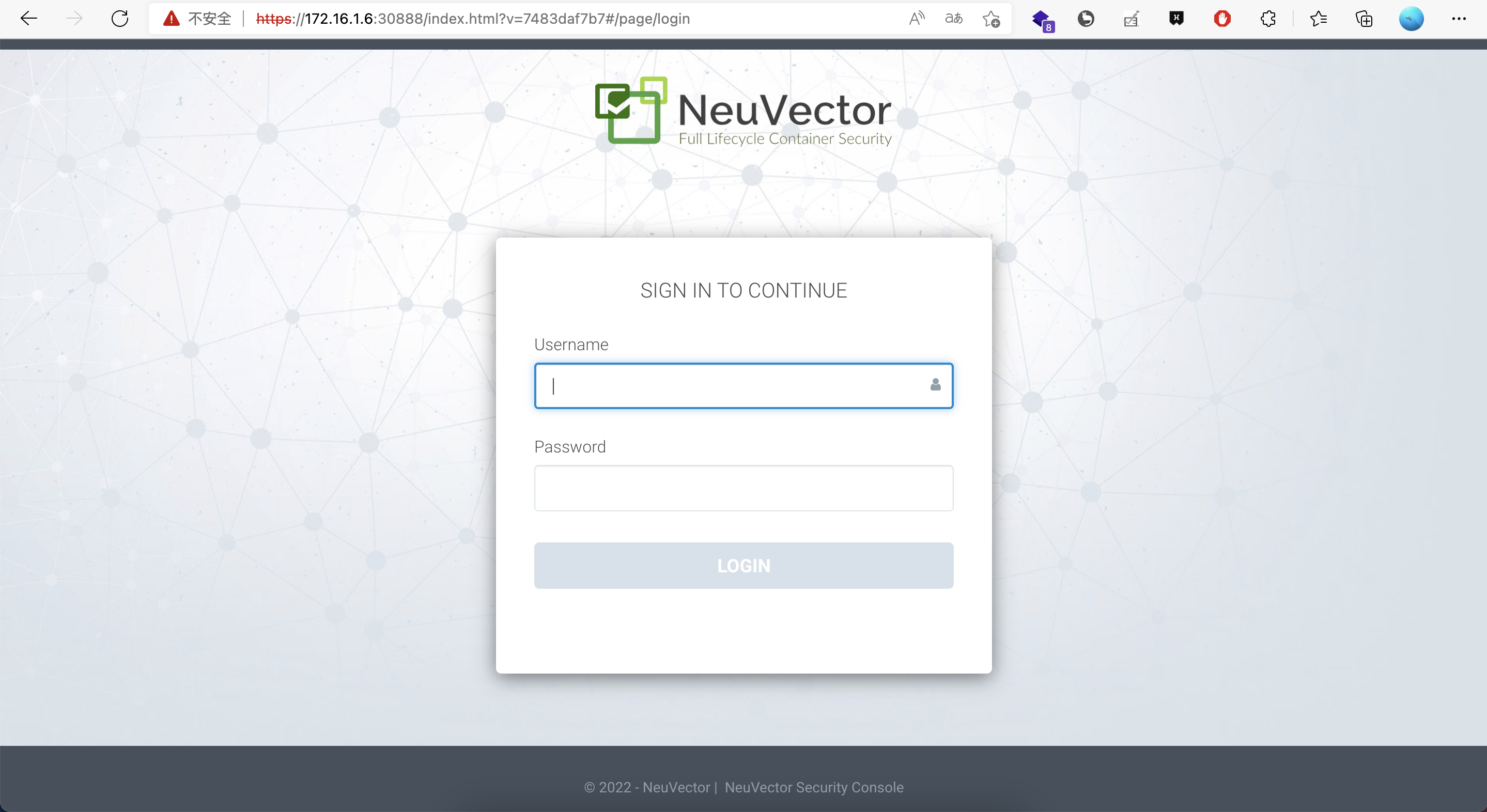
Helm部署
添加repo
helm repo add neuvector https://neuvector.github.io/neuvector-helm/
helm search repo neuvector/core
创建namespace
kubectl create namespace neuvector
创建ServiceAccount
kubectl create serviceaccount neuvector -n neuvector
helm安装
helm install neuvector --namespace neuvector neuvector/core --set registry=docker.io --set tag=5.0.0-preview.1 --set=controller.image.repository=neuvector/controller.preview --set=enforcer.image.repository=neuvector/enforcer.preview --set manager.image.repository=neuvector/manager.preview --set cve.scanner.image.repository=neuvector/scanner.preview --set cve.updater.image.repository=neuvector/updater.preview
Helm-chart参数查看
https://github.com/neuvector/neuvector-helm/tree/master/charts/core
高可用架构设计

NeuVector-HA主要需要考虑Controller模块的HA,只要有一个Controller处于打开状态,所有数据都将在3个副本之间之间同步。
Controller数据主要存储在 /var/neuvector/ 目录中,但出现POD重建或集群重新部署时,会自动从此目录加载备份文件,进行集群恢复。
部署策略
NeuVector官方提供四种HA部署模式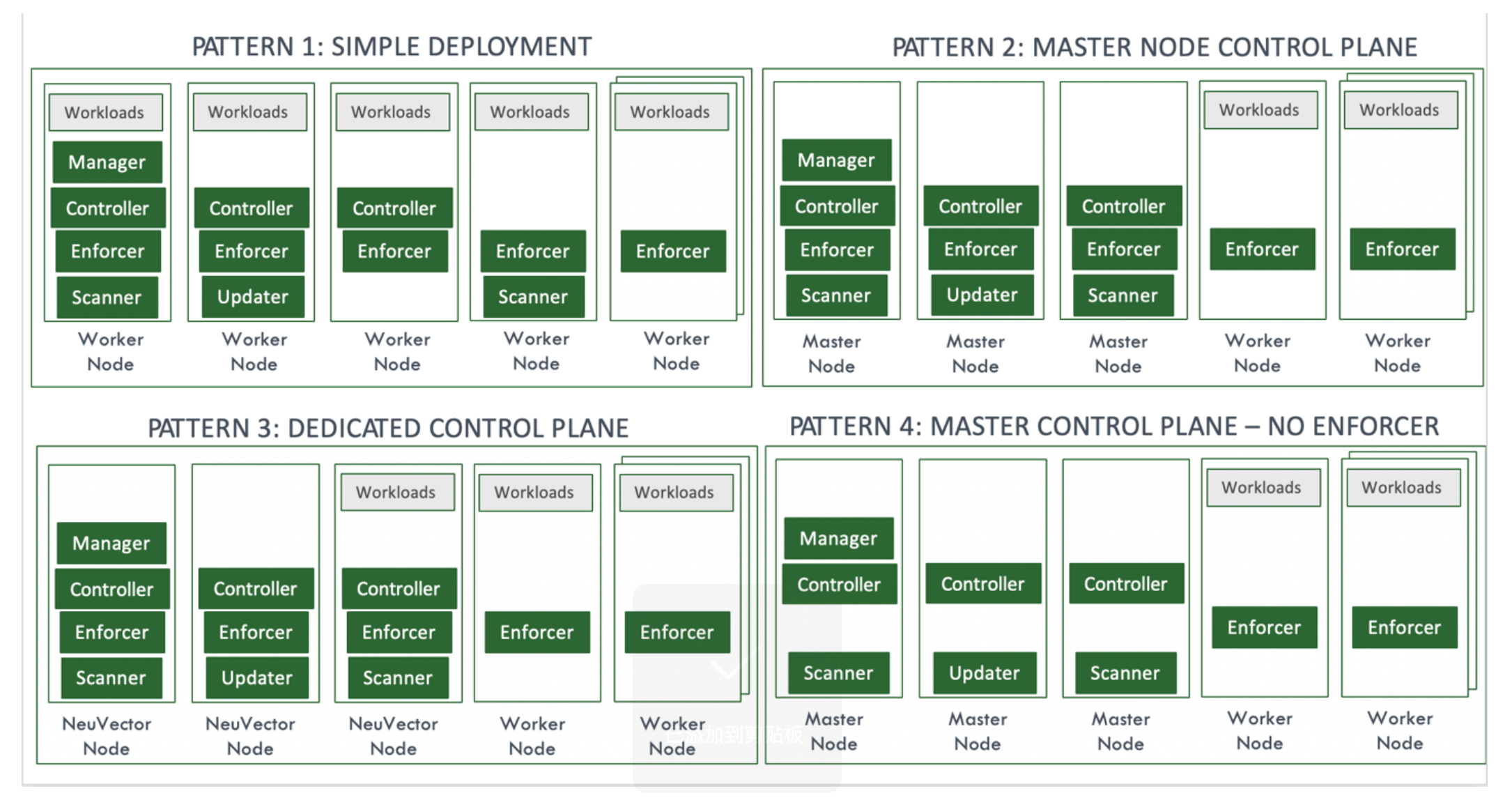
方式一:不进行任何调度限制,由Kubernetes进行自由调度管理管理。
方式二:NeuVector control组件(manager,controller)+enforce、scanner组件配置调度label限制和污点容忍,与Kubernetes master节点部署一起。
方式三:给Kubernetes集群中通过Taint方式建立专属的NeuVector节点,只允许NeuVector control组件部署。
方式四:NeuVector control组件(manager,controller)配置调度label限制和污点容忍,与Kubernetes master节点部署一起。k8s-master不部署enforce和scanner组件,意味着master节点不在接受扫描和策略下发。
以方式二为例,进行部署
给master节点打上特定标签
kubectl label nodes nodename nvcontroller=true
获取节点Taint
kubectl get node nodename -o yaml|grep -A 5 taint
以rancher部署的节点master节点为例
taints:
- effect: NoSchedule
key: node-role.kubernetes.io/controlplane
value: "true"
- effect: NoExecute
key: node-role.kubernetes.io/etcd
编辑部署的yaml给NeuVector-control组件(manager,controller)添加nodeSelector和tolerations给enforce、scanner组件只添加tolerations。
例如以manager组件为例:
kind: Deployment
metadata:
name: neuvector-manager-pod
namespace: neuvector
spec:
selector:
matchLabels:
app: neuvector-manager-pod
replicas: 1
template:
metadata:
labels:
app: neuvector-manager-pod
spec:
nodeSelector:
nvcontroller: "true"
containers:
- name: neuvector-manager-pod
image: neuvector/manager.preview:5.0.0-preview.1
env:
- name: CTRL_SERVER_IP
value: neuvector-svc-controller.neuvector
restartPolicy: Always
tolerations:
- effect: NoSchedule
key: "node-role.kubernetes.io/controlplane"
operator: Equal
value: "true"
- effect: NoExecute
operator: "Equal"
key: "node-role.kubernetes.io/etcd"
value: "true"
数据持久化
配置环境变量启用配置数据持久化
- env:
- name: CTRL_PERSIST_CONFIG
配置此环境变量后,默认情况下Neuvector-Controller会将数据存储在/var/neuvector目录内,默认此目录是hostpath映射在POD所在宿主机的/var/neuvector目录内。
若需要更高级别数据可靠性也可以通过PV对接nfs或其他支出多读写的存储中。
这样当出现Neuvector-Controller三个POD副本同时都销毁,宿主机都完全不可恢复时,也不会有数据配置数据丢失。
以下以NFS为例。
部署nfs
创建pv和pvc
cat <<EOF | kubectl apply -f -
apiVersion: v1
kind: PersistentVolume
metadata:
name: neuvector-data
spec:
capacity:
storage: 10Gi
accessModes:
- ReadWriteMany
nfs:
path: /nfsdata
server: 172.16.0.195
EOF
cat <<EOF | kubectl apply -f -
kind: PersistentVolumeClaim
apiVersion: v1
metadata:
name: neuvector-data
namespace: neuvector
spec:
accessModes:
- ReadWriteMany
resources:
requests:
storage: 10Gi
EOF
修改NeuVector-Controller部署yaml,添加pvc信息,将/var/neuvector目录映射到nfs中(默认是hostpath映射到本地)
spec:
template:
spec:
volumes:
- name: nv-share
# hostPath: // replaced by persistentVolumeClaim
# path: /var/neuvector // replaced by persistentVolumeClaim
persistentVolumeClaim:
claimName: neuvector-data
或直接在NeuVector部署yaml中挂载nfs目录
volumes:
- name: nv-share
nfs:
path: /opt/nfs-deployment
server: 172.26.204.144
多云安全管理
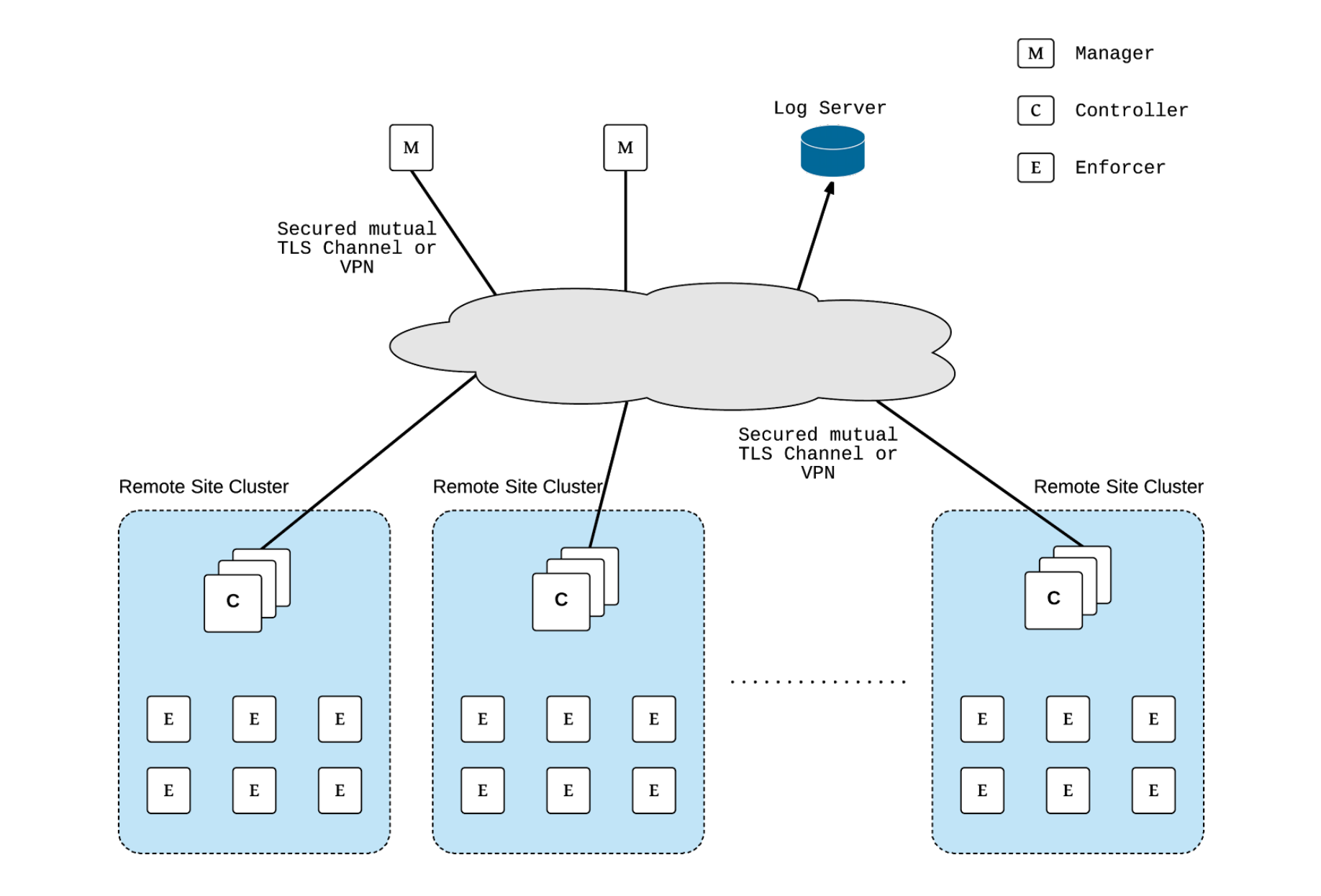
在实际生产应用中,会存在对多个集群进行安全进行管理,NeuVector支持集群联邦功能。
需要在一个集群上暴露Federation Master服务,在每个远端集群上部署Federation Worker服务。为了更好的灵活性,可以在每个集群同时启用Federation Master和Federation Worker服务。
在每个集群部署此yaml
apiVersion: v1
kind: Service
metadata:
name: neuvector-service-controller-fed-master
namespace: neuvector
spec:
ports:
- port: 11443
name: fed
nodePort: 30627
protocol: TCP
type: NodePort
selector:
app: neuvector-controller-pod
---
apiVersion: v1
kind: Service
metadata:
name: neuvector-service-controller-fed-worker
namespace: neuvector
spec:
ports:
- port: 10443
name: fed
nodePort: 31783
protocol: TCP
type: NodePort
selector:
app: neuvector-controller-pod
将其中一个集群升级为主集群
将其中一个集群升级为主集群,配置连接远程暴露ip和对remot cluster可达的端口。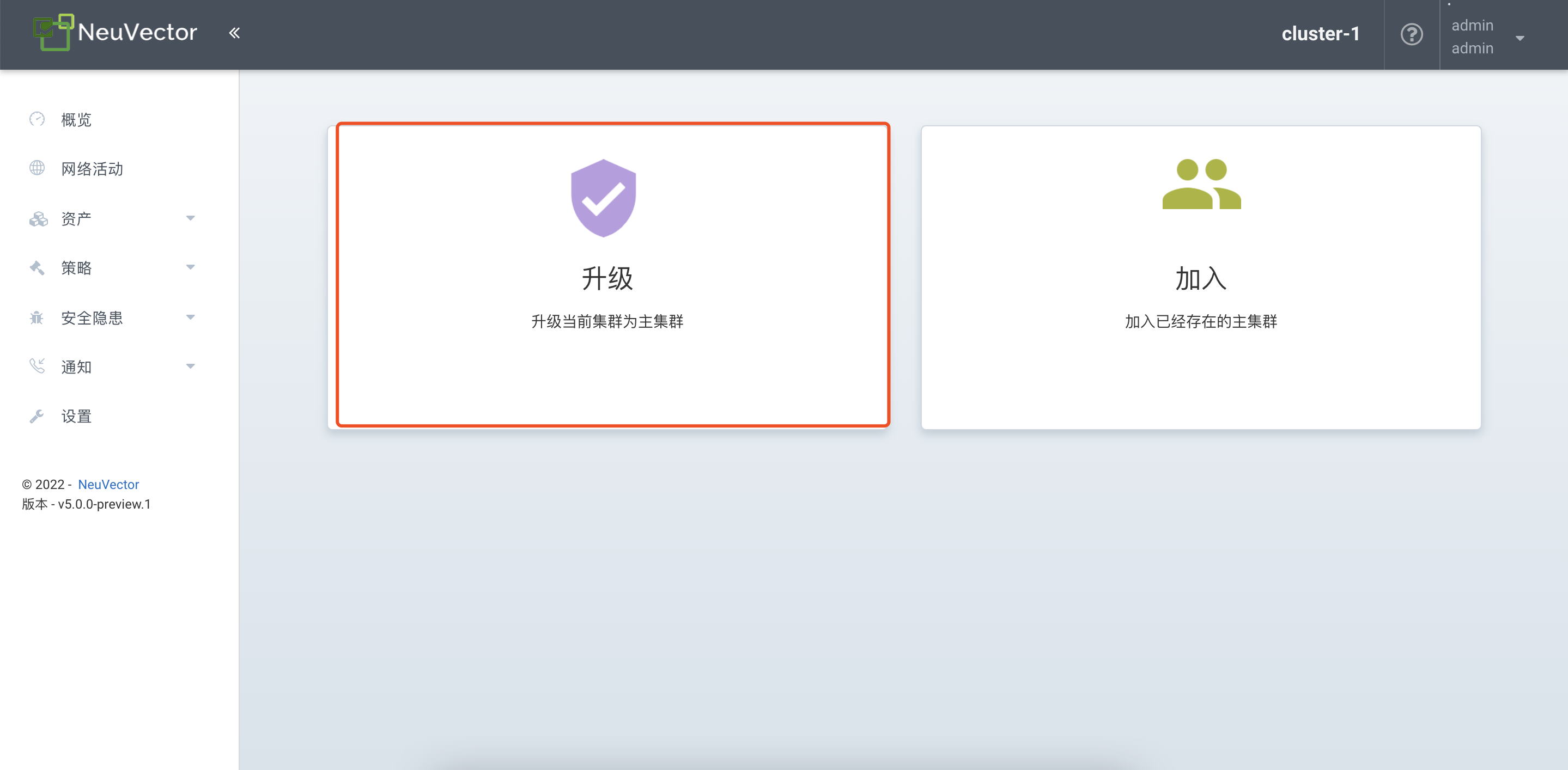
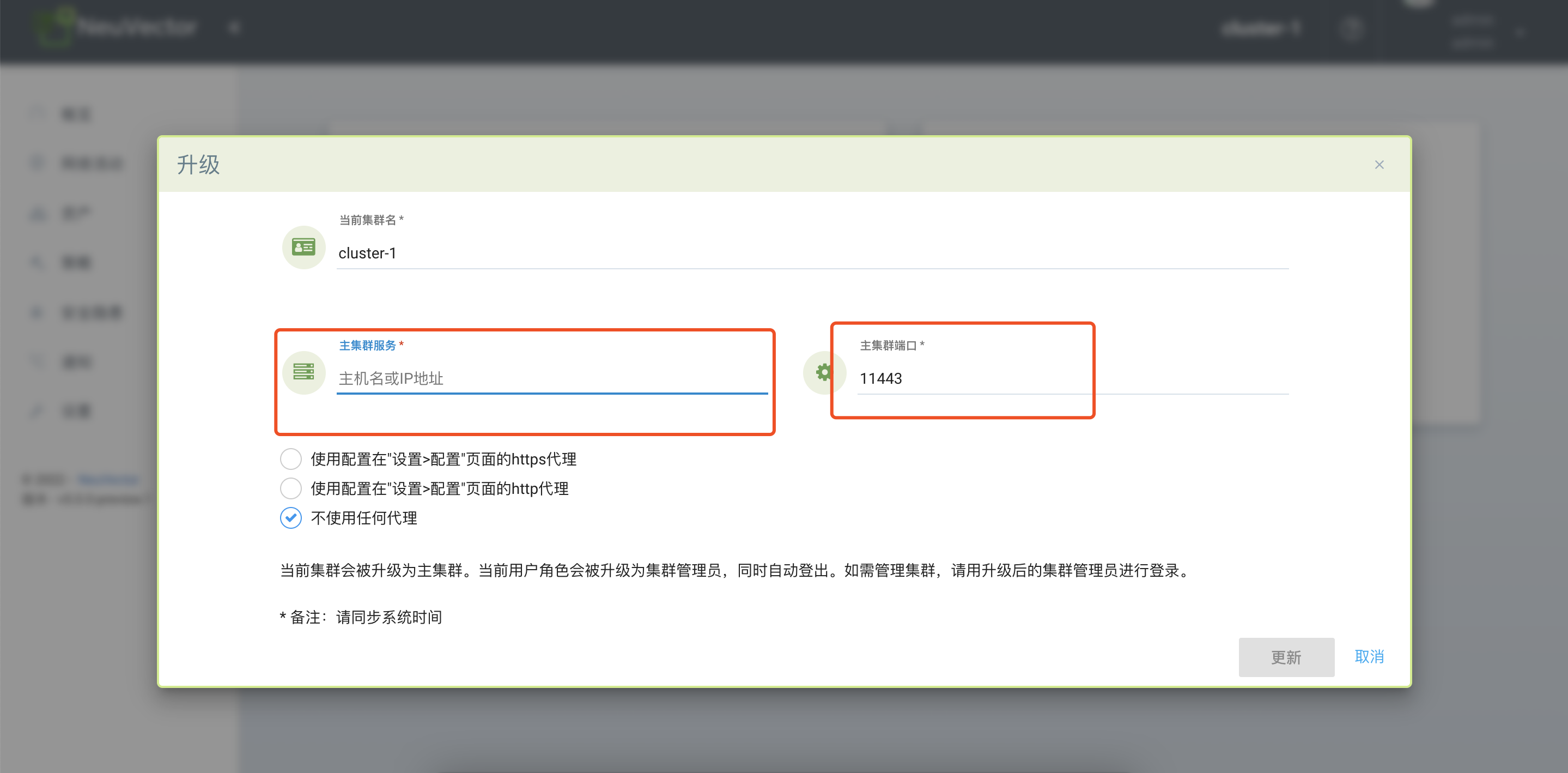

在主集群中,生成token,用于其他remote cluster连接。
在remote cluster中配置加入主集群,配置token和连接端子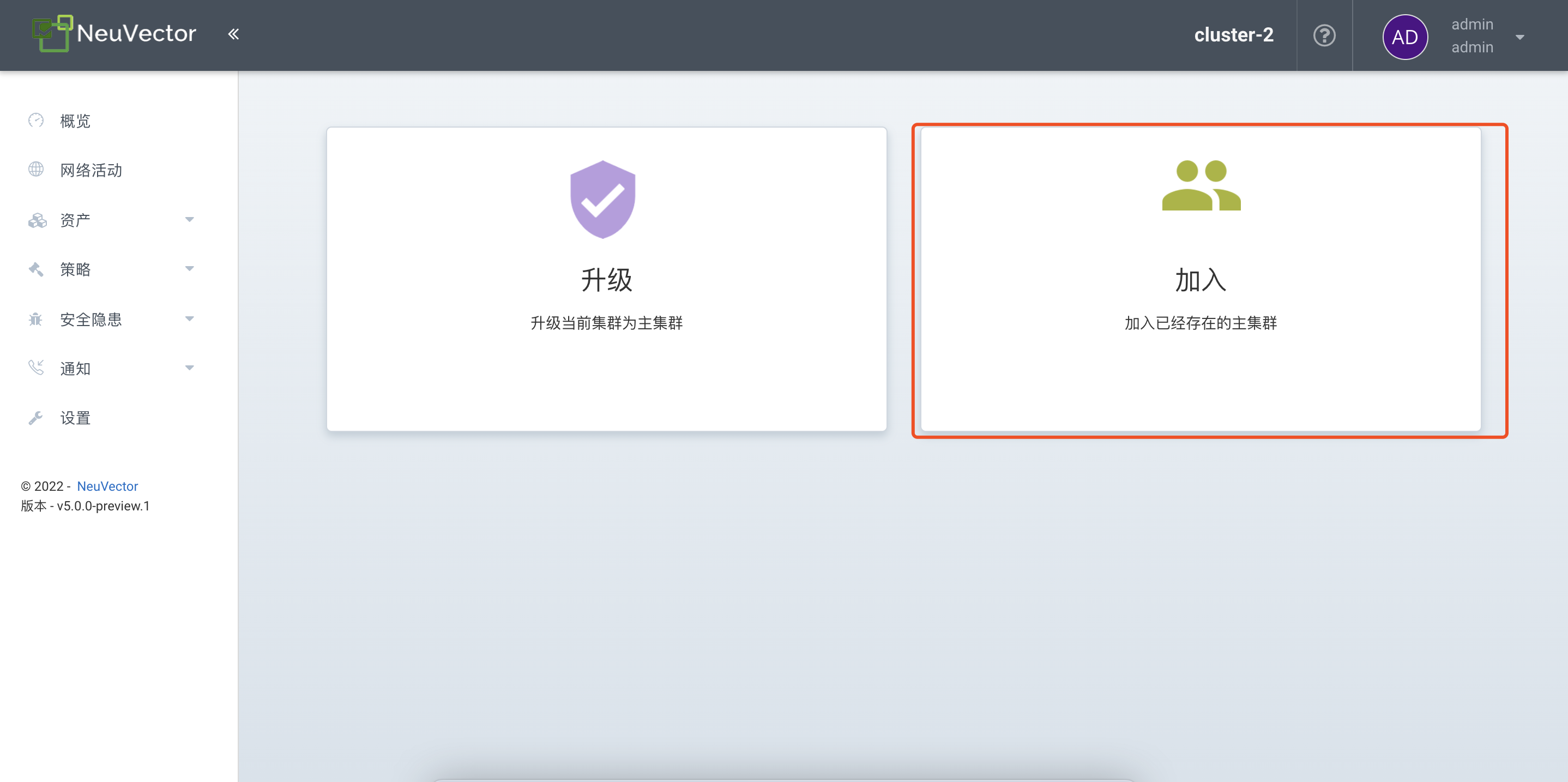
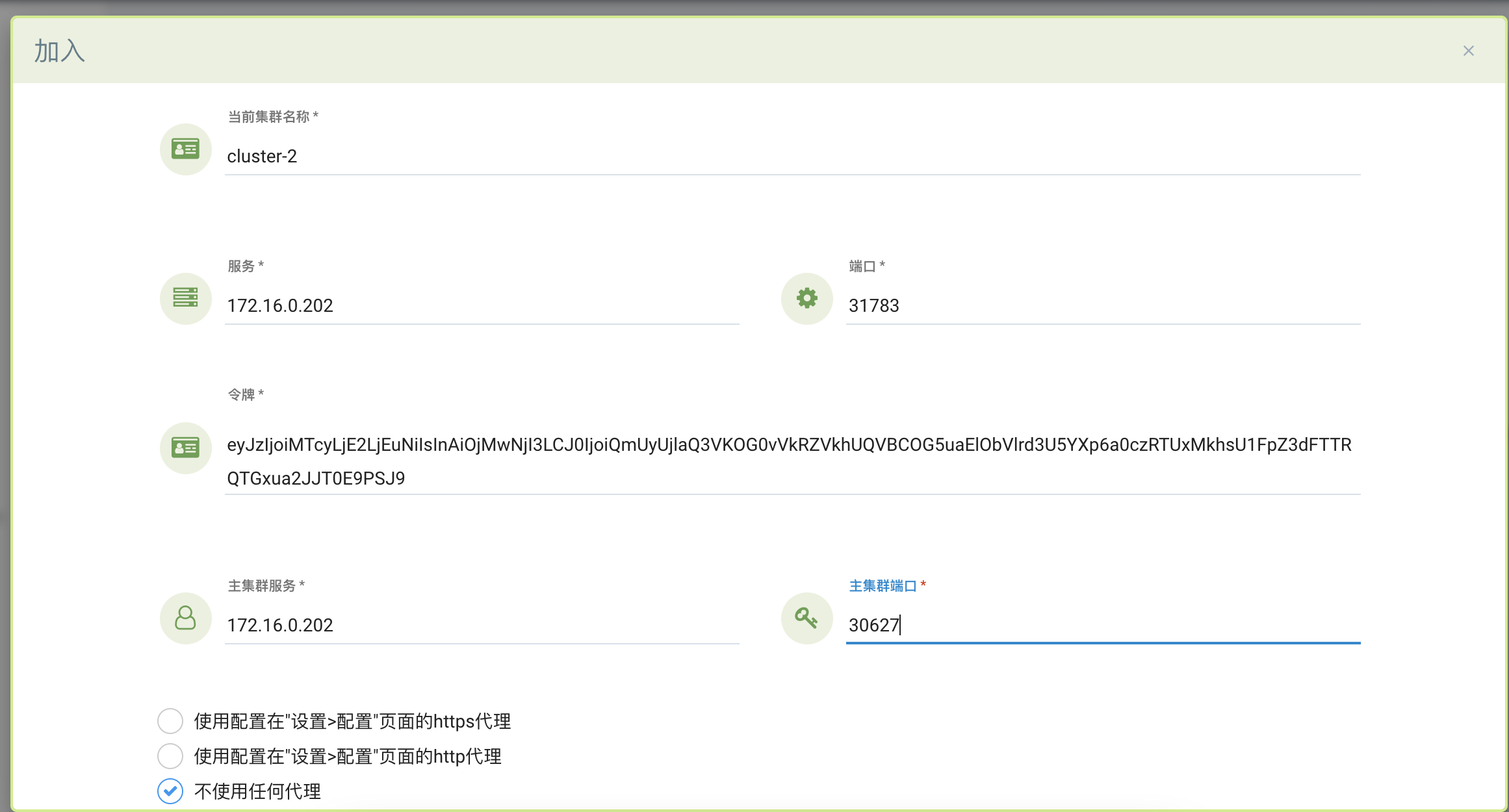
在界面可以对多个Neuvector集群进行管理
其他配置
升级
若是采用yaml文件方式部署的NeuVector直接更新对应的组件镜像tag即可完成升级。如
kubectl set image deployment/neuvector-controller-pod neuvector-controller-pod=neuvector/controller:2.4.1 -n neuvector
kubectl set image -n neuvector ds/neuvector-enforcer-pod neuvector-enforcer-pod=neuvector/enforcer:2.4.1
若是采用Helm部署的NeuVector,则直接执行helm update配置对应参数即可即可。
卸载
删除部署的组件
kubectl delete -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/neuvector-docker-k8s.yaml
删除配置的RBAC
kubectl get clusterrolebinding | grep neuvector|awk '{print $1}'|xargs kubectl delete clusterrolebinding
kubectl get rolebinding -n neuvector | grep neuvector|awk '{print $1}'|xargs kubectl delete rolebinding -n neuvector
删除对应的CRD
kubectl delete -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/crd-k8s-1.19.yaml
kubectl delete -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/waf-crd-k8s-1.19.yaml
kubectl delete -f https://raw.githubusercontent.com/neuvector/manifests/main/kubernetes/5.0.0/admission-crd-k8s-1.19.yaml
总结:
SUSE此次开源的NeuVector是一个成熟稳定的容器安全管理平台,未来NeuVector会和Rancher产品更好的融合。